Post #406,002
11/5/15 6:06:51 PM
|

WP: Linus on Linux kernel security and more.
Washington Post. It's aimed at a lay-audience, so a lot of it is dumbed down. But it's still interesting. I'm not sure I agree with this though: Even without a potential nuclear disaster, the stakes are high. Operating system kernels are the most essential code on any computer, allowing hardware to work smoothly with multiple pieces of software. This makes kernels uniquely powerful — they can override the safeguards on any other program, meaning nothing on a computer is truly secure if the operating system kernel is not. A kernel is designed to let other programs run and access the machine. The phrasing seems to imply that a kernel can break the security of running programs. That seems nonsensical to me. A virus isn't a kernel, and an infect kernel is a kernel running a virus - not kernel itself. That last sentence tells you the slant of the article. Any system that allows writing to memory is a potentially insecure. I believe it's been proven that you cannot have a system that can be verified to be virus-proof. (I.e. checking for virus signatures only goes so far - what if the list is changed? Etc.) (via Mary Zeman on G+) Cheers, Scott.
|
Post #406,006

11/5/15 7:49:41 PM
|

Re: WP: Linus on Linux kernel security and more.
Well, that sucks. Can't view a G+ post unless signed in to Google.
Strike one more thing from the short list of "reasons G+ is better than Facebook".
|
Post #406,008
11/5/15 8:41:44 PM
|

Interesting. I wonder how new that is. :-(
|
Post #406,009
11/5/15 10:22:29 PM
11/5/15 10:23:16 PM
|

I believe it's been proven that you cannot have a system that can be verified to be virus-proof.
hogwash, we were doing it in the 1990s and can still do it
build a *nix off of the network with preselected network routing info with no hd only a readonly floppy/usb stick
remove uid 0
(edit added a wrong step)
Good luck breaking into that you can kill people for America at age 18 but need to be 21 to buy a beer

Edited by boxley
Nov. 5, 2015, 10:23:16 PM EST
|
Post #406,012

11/5/15 10:39:55 PM
|

And don't turn it on
|
Post #406,013
11/5/15 10:41:10 PM
|

Fred Cohen in 1987.
An Undetectable Computer Virus (8 page .pdf): One of the few solid theoretical results in the study of computer viruses is Cohen's 1987 demonstration that there is no algorithm that can perfectly detect all possible viruses [1]. This brief paper adds to the bad news, by pointing out that there are computer viruses which no algorithm can detect, even under a somewhat more liberal definition of detection. We also comment on the senses of "detect" used in these results, and note that the immediate impact of these results on computer virus detection in the real world is small. Yes, there are ways to keep computers from being infected under most circumstances, but you cannot make - and prove - that a computer system is virus-proof. HTH. Cheers, Scott.
|
Post #406,015

11/5/15 10:48:39 PM
|

And that only works if you trust the compiler, too. :-)
Regards,
-scott
Welcome to Rivendell, Mr. Anderson.
|
Post #406,017
11/5/15 10:52:05 PM
|

back in those days we built the compilers :-)
you can kill people for America at age 18 but need to be 21 to buy a beer
|
Post #406,021

11/5/15 11:40:14 PM
|

Ah, but what did you compile them with?
Regards,
-scott
Welcome to Rivendell, Mr. Anderson.
|
Post #406,024
11/5/15 11:53:13 PM
|

Oooh. Nice. Thanks muchly. (Interesting comments too.)
|
Post #406,027
11/6/15 12:32:32 AM
|

assembler, required for a cs degree in 1992
had to do the boss's wifes homework. you can kill people for America at age 18 but need to be 21 to buy a beer
|
Post #406,029

11/6/15 2:00:28 AM
|

Who wrote the assembler?
You didn't construct the executable image by hand in a hex editor.
But if you did, who wrote the hex editor?
Turtles all the way down!
|
Post #406,036

11/6/15 9:18:50 AM
|

Beat me to it.
Regards,
-scott
Welcome to Rivendell, Mr. Anderson.
|
Post #406,038
11/6/15 10:05:46 AM
|

FTW!
|
Post #406,049
11/6/15 12:10:59 PM
|

I wrote the assembler for the machine code but ya got me using a hex editor
you can kill people for America at age 18 but need to be 21 to buy a beer
|
Post #406,052

11/6/15 12:48:10 PM
|

Did you poke the holes out of the paper tape with a pin? No? Pussy
|
Post #406,054
11/6/15 12:49:46 PM
|

that was before my time sorry
you can kill people for America at age 18 but need to be 21 to buy a beer
|
Post #406,057

11/6/15 1:59:33 PM
|

Where does using a Flexowriter fit?
Friden Flexowriter. You hit typewriter keys and it punches the holes in paper tape. Using manual paper tape punch was only used for editing. My first bit of code was machine code (homework assignment without benefit of assembler) and we did that in octal (not hex). The machine had an 18-bit word architecture, so it took 6 octal digits to specify a word. So, the code would have looked something like this: 145703 342521 231453 ... The professor wanted us appreciate the convenience of an assembler! Alex
"There is a cult of ignorance in the United States, and there has always been. The strain of anti-intellectualism has been a constant thread winding its way through our political and cultural life, nurtured by the false notion that democracy means that "my ignorance is just as good as your knowledge."
-- Isaac Asimov
|
Post #406,058

11/6/15 2:02:11 PM
|

You ... win?
Not quite sure that's the right word for that.
|
Post #406,061
11/6/15 2:39:54 PM
|

Alex and Skip win all those argies hands down
you can kill people for America at age 18 but need to be 21 to buy a beer
|
Post #406,068
11/6/15 4:32:57 PM
|

:-)
My first "program" (to brute-force find and print prime numbers) was on a teletype with a paper tape punch/reader. 300 baud FTW!
Neat story! I hope you're documenting these things in more detail somewhere! :-)
Cheers,
Scott.
|
Post #406,069

11/6/15 6:50:35 PM
|

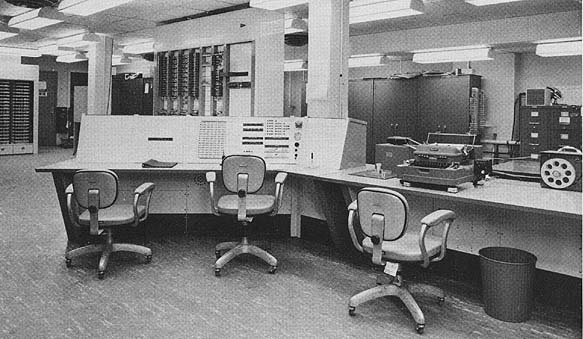
Well, it was the TX-0 computer, and a historical machine.
Computer History Museum. 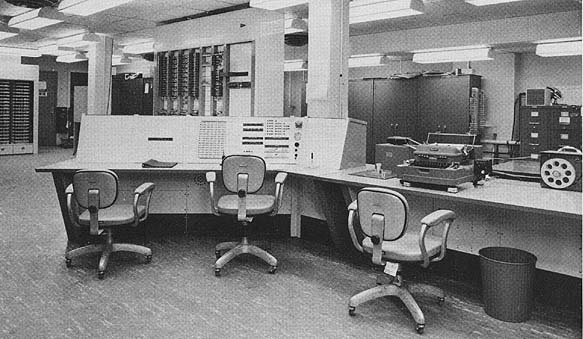 It was the first computer to ever use both transistors for the circuitry and ferrite cores for memory. It was a single copy, proof of concept, machine built at MIT Lincoln Labs. It was a re-implementation of the vacuum tube based Whirlwind computer. Originally with 64 K words, it was downgraded to 4 K words when given to MIT's EE department. That original memory was redeployed in the MIT Lincoln Lab's TX-2 computer a 36-bit machine. As a side note, note the rectangular gray area to the left of the middle chair's backrest. That is an array of 16 x 18 toggle switches which coded the "boot loader" i.e. a bit like BIOS. The circuit designer was Ken Olson who, soon after the TX-2 project, started DEC (Digital Equipment Corp) and started making and selling the PDP-1 computer. Ken was good enough to give a PDP-1 to MIT. It was across the hall from my office, so I got to play with it on occasion. Alex
"There is a cult of ignorance in the United States, and there has always been. The strain of anti-intellectualism has been a constant thread winding its way through our political and cultural life, nurtured by the false notion that democracy means that "my ignorance is just as good as your knowledge."
-- Isaac Asimov
|
Post #406,072
11/6/15 8:31:00 PM
|

Just the compiler?
|
Post #406,020
11/5/15 11:29:19 PM
|

Not quite nonsensical
Malware running in kernel mode has free access to everything. If it can inject itself in a driver chain, all data that flows trough there is accessible.
But implying Linux was the enabling cause of the Ashley Madison hack is pure FUD. Nothing definite about the breach point has been released, AFAIK, but if the perps are to be believed, the root account password on all servers was Pass1234. With friends like that, you do not need kernel vulnerabilities :-/
|
Post #406,022

11/5/15 11:41:34 PM
|

O_o
I know it wasn't a financial system, but seriously...? Because no-one would ever want to hack into something like that...
smh... Regards,
-scott
Welcome to Rivendell, Mr. Anderson.
|
Post #406,025
11/5/15 11:59:04 PM
|

Sure, but...
This is a semantic argument on my part, and maybe I've got it wrong, but I would argue that a virus running in a protected kernel mode on a processor is still a virus and not a kernel itself. Maybe the author had to try to simplify the discussion, but the way I read what was written is (roughly):
"Because Linus is stubborn and in over his head when it comes to security, his kernel can take over a nuclear power plant and kill millions of people."
:-/
The password thing is all too believable...
Thanks.
Cheers,
Scott.
|
Post #406,030

11/6/15 2:01:54 AM
|

Why even bother hacking the kernel?
That's hard - both to do and to exploit once you've done it.
Much easier to rely on the fact that either the application stack is vulnerable or, even more likely, a human being fucked things up.
|
Post #406,071
11/6/15 8:19:22 PM
|

Indeed
|